1. For those of you who have started reading this post coz of the tempting post title claiming extracting username/passwords from a RAM Dump,I must assure you it is possible easily in few steps using Volatility Framework.In the post ahead I have a RAM dump of a Windows 7 OS and I have been able to extract the user names and passwords of these users in three simple steps using Volatility Framework.Well,I will quickly get to the steps with screenshots :
Setup Required
- Volatility Framework Installed.[How to Install at http://anupriti.blogspot.in/2015/09/volatility-advanced-memory-forensics.html]
- Taking Ram Dump from Windows
[How to take RAM dump at para 3 of http://anupriti.blogspot.in/2015/09/volatility-command-using-imageinfo-to.html]
Here I am using two commands basically ie hivelist and hashdump
HIVELIST
Hivelist is used to locate the virtual addresses of registry hives in memory, and the full paths to the corresponding hive on disk.
Command Usage
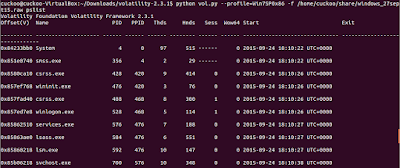
python vol.py --profile=Win7SP0x86 -f /home/cuckoo/Desktop/windows_7_ramdump.raw hivelistYou get a similar output as seen below :
 |
| CLICK TO ENLARGE |
 |
| Note Virtual Address for SYSTEM as highlighted CLICK TO ENLARGE |
 |
| Note Virtual Address for SAM as highlighted CLICK TO ENLARGE |
HASHDUMP
Hashdump is used to extract and decrypt cached domain credentials stored in the registry.
Command Usage
To use hashdump, pass the virtual address of the SYSTEM hive as -y and the virtual address of the SAM hive as -s, as shown below:python vol.py --profile=Win7SP0x86 hashdump -f /home/cuckoo/Desktop/windows_7_ramdump.raw -y 0x8901a360 -s 0x8faff008
 |
| Hashdump output seen with user names and NTLM dump CLICK TO ENLARGE |
DECRYPTING NTLM hash
Now comes decrypting this hash as we have got vide hashdump above.Hashes can now be cracked using John the Ripper, rainbow tables, etc.Now no need to install these crackers separately.Simply google for online decryptos and you will get the password too.I used this site at http://www.hashkiller.co.uk/ntlm-decrypter.aspxScreen shots below:
 |
| Password extracted is test_1234 CLICK TO ENLARGE |
 |
| Password extracted is test_123 CLICK TO ENLARGE |
 |
| Password extracted is test CLICK TO ENLARGE |
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246